This is a multi-page, printable view of this section. Click here to print.
Cyber City Mansion
1 - How to Prevent Personal Information Leaks and "Doxxing" Risks
Beware of Risks from Piecing Together Fragmented Information
In the internet era, personal information exists in fragmented forms across various platforms and services. Many people believe that leaking bits of information is inconsequential. However, the online environment is not absolutely safe, and individuals with malicious intent can collect and integrate these fragmented pieces to create a complete personal profile. Even the simplest search engine can be used for information gathering.
Taking a certain social platform as an example, while users share snippets of their lives, they may inadvertently expose personal information. For instance, some users enjoy publicly discussing the meaning and usage scenarios of passwords, which undoubtedly increases the risk of password cracking.
The principles of social engineering tell us that meaningful strings often appear repeatedly in multiple places. A unique username or an easily remembered password is likely to be reused by users across different platforms, becoming a common pathway for internet information leaks.
Reduce Account Association to Protect Personal Identity
For the average internet user, if there is no need to build a personal brand, it is recommended to use randomly generated usernames and passwords to minimize the association between accounts on different platforms.
It should be noted that using different account passwords alone is not enough to completely eliminate account association. If similar or identical content is posted across different platform accounts, it may still be possible to identify the association.
Common Types of Sensitive Information
Here are some common types of sensitive information that require special attention to protect:
- Passwords
- Usernames
- Profile pictures
- Birthdays
- Addresses
- Phone numbers
- Email addresses
- QQ numbers
- WeChat IDs
- Personal websites
- Geographic locations
- Photos
Some criminals use “social engineering databases” to integrate personal information leaked from different channels. For example, if information leaked from two different platforms contains the same phone number, it can be highly suspected that these two pieces of information belong to the same person.
Even if usernames and photo styles from different platforms are vastly different, they may still be linked through social engineering databases, ultimately forming a complete personal information file.
This is not an exaggeration but a common application scenario of social engineering databases. The threshold for using social engineering databases for information collection and “doxxing” is not high, and even minors can easily master it.
Enhance Cybersecurity Awareness to Protect Personal Privacy
While the internet brings people closer together, it can also exacerbate the distance between them. Social platforms provide a space for communication but may also make people feel more isolated.
In the online world, we yearn to express ourselves and find resonance, but we also need to remain vigilant and protect our personal privacy.
When interacting with strangers online, there is no need to disclose personal information in detail. Be cautious in speech and action, maintain restraint, enjoy solitude, and improve oneself to navigate the online world with ease.
Recommendations:
- Regularly check and update your passwords to ensure they are strong enough.
- Avoid using the same account passwords across different platforms.
- Be cautious when sharing photos and updates that contain personal information.
- Use tools like AdGuardPrivate to protect your DNS queries and prevent DNS leaks.
- Stay informed about the latest cybersecurity trends and promptly learn about new threats and prevention methods.
2 - Guide to Protecting Personal Online Privacy
Why Protect Online Privacy?
In the digital age, every online activity can leave a trace:
- Browsing history is tracked
- Personal preferences are analyzed
- Location information is collected
- Social relationships are mapped
Basic Protection Measures
1. Browser Configuration
- Use private browsing mode
- Disable third-party cookies
- Enable “Do Not Track” feature
- Regularly clear browsing data
2. Search Engine Selection
- Use anonymous search engines (like DuckDuckGo)
- Avoid searching sensitive content while logged in
- Use multiple search engines for cross-verification
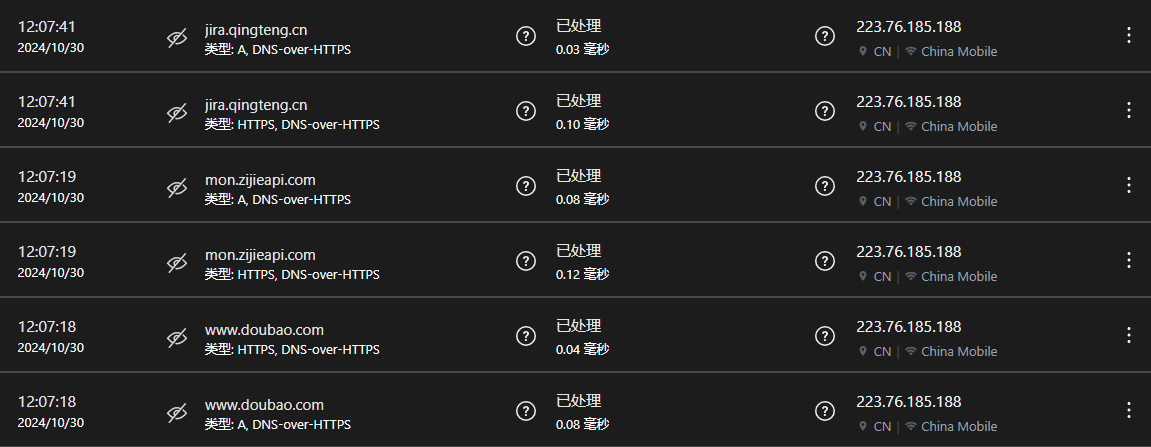
3. DNS Encryption Protection
- Enable DNS-over-HTTPS
- Use private DNS services
- Avoid default DNS servers
Advanced Protection Strategies
1. Network Access Protection
- Use trusted services
- Enable HTTPS-Only mode
- Avoid using public Wi-Fi
2. Ad Tracking Protection
- Install ad blockers
- Use content filters
- Turn off personalized ad options
3. Social Media Privacy
- Review privacy settings
- Limit sharing of personal information
- Turn off location services
- Be cautious with third-party logins
Daily Use Recommendations
Reduce Digital Footprint
- Use temporary email services
- Avoid registering with real names
- Use different passwords on different platforms
- Regularly check authorized applications
Prevent Privacy Leaks
- Use password managers
- Enable two-factor authentication
- Encrypt important files
- Be cautious when installing new apps
Precautions
- Use privacy protection tools reasonably
- Comply with local laws and regulations
- Keep software updated
- Cultivate privacy protection awareness
Complete anonymity is difficult to achieve, but these measures can significantly enhance personal privacy protection. Choose the protection measures that suit you, finding a balance between convenience and security.
3 - Guidelines for Protecting Adolescents' Online Safety
Challenges in the Online Environment for Modern Adolescents
In the digital age, adolescents face unprecedented online challenges:
- Vast amounts of information of varying quality
- Limited ability to identify online risks
- Easily attracted to harmful content
- Lack of self-management awareness
Intelligent Protection Solutions
1. Application Access Management
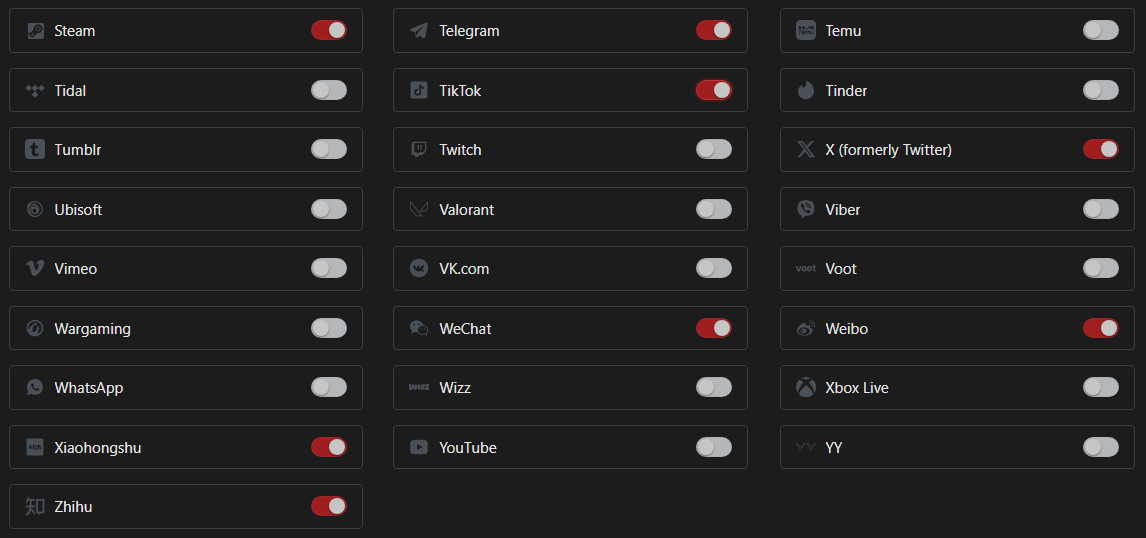
Features:
- Precise control over accessible applications
- Prevent installation of inappropriate software
- Protect personal information security
2. Time Management System
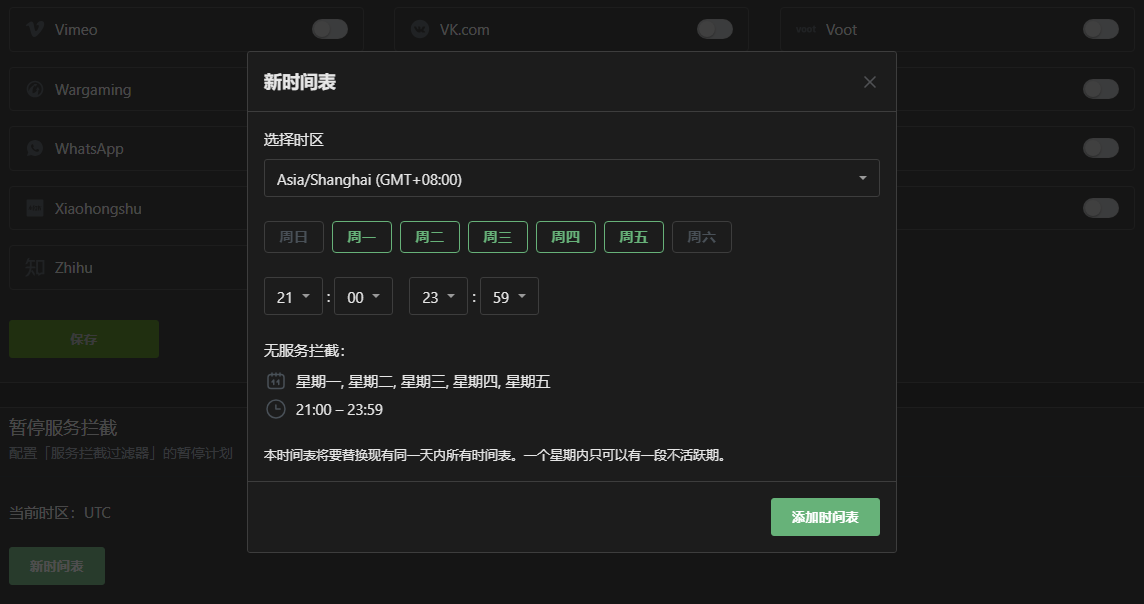
Functions:
- Set reasonable usage periods
- Prevent internet addiction
- Foster good sleep habits
3. Behavior Monitoring and Guidance
Access Record Analysis
Uses:
- Understand online behavior patterns
- Timely identify potential risks
- Provide targeted guidance and communication
Intelligent Interception Settings

Customizable:
- Content rating filtering
- Personalized protection rules
- Dynamic adjustment of strategies
Parental Guidance Suggestions
Beyond protective measures, good family education is even more important:
- Have open conversations with children about internet use
- Cultivate independent thinking and judgment skills
- Establish a trusting communication mechanism
- Gradually relax controls
Technological means are auxiliary tools; education and guidance are fundamental. Use control tools appropriately while focusing on cultivating adolescents’ internet literacy and self-management abilities.
4 - Protecting Seniors from Online Scams
Online Risks Faced by Seniors
In today’s society, seniors are facing increasingly serious cybersecurity threats. The following characteristics make them a high-risk group for online scams:
- Not proficient in operating smartphones
- Lack of awareness and prevention of online scams
- Less exposure to cybersecurity-related information
- Easily trust unverified software download links
Technical Protection Solutions
AdGuard Security Protection
AdGuard provides professional malware interception functionality:

This solution has the following advantages:
- Runs in the cloud, no need to install additional applications
- Zero system resource consumption
- Simple configuration and not easily misoperated
- Automatic continuous protection
Practical Effects
After a year of practice, we have observed significant improvements:
- Significantly reduced requests for “phone cleaning” assistance
- Enhanced daily usage experience
- Reduced phone usage frustrations
Comprehensive Protection Strategy
While technical measures are important, comprehensive protection also requires:
- Regular companionship and communication to understand usage difficulties
- Patiently explaining basic cybersecurity knowledge
- Staying vigilant and promptly identifying potential threats
Technology is a tool, but care is the foundation. Regular companionship and patient guidance are the best ways to protect seniors from online risks.
5 - How to Deal with Corporate Network Monitoring
The Evolution of Corporate Network Monitoring
The monitoring methods of modern enterprises have shifted from traditional physical monitoring (such as cameras, on-site inspections, etc.) to more sophisticated digital monitoring systems. This transition makes monitoring more covert and cost-effective.
Common Network Monitoring Methods
One of the core methods of corporate network monitoring is tracking through DNS servers. The specific implementation methods include:
- Deploying dedicated DNS servers within the corporate network
- Forcing the use of corporate DNS through DHCP services
- Establishing a correspondence between IP addresses and workstations
The Technical Principles of Monitoring
Even today, with the widespread use of HTTPS, DNS queries are still transmitted in plain text. This means:
- All domain name resolution requests will be recorded
- Although the specific content accessed cannot be seen, the domain names of the websites visited can be known
- Combined with timestamps, employee internet behavior patterns can be analyzed
Solutions for Protecting Personal Privacy
To reasonably protect personal privacy, consider the following solutions:
- Use personal mobile networks
- Configure private DNS services
- Use secure VPN services
Please note: When taking any privacy protection measures, one should comply with relevant laws and regulations and corporate policies.